Blank Grabber
Blank Grabber
A “Blank Grabber” is not a well-known or widely recognized term in the context of malware. However, I can provide you with a general overview of what a malware is and explain the potential elements and functionalities that a malware might include.
Malware Overview: Malware, short for “malicious software,” refers to a broad category of software programs or code that is specifically designed to infiltrate and harm computer systems, networks, or user data. Malware can come in various forms, and its objectives can range from stealing sensitive information to disrupting computer operations or even causing financial harm. Some common types of malware include viruses, worms, Trojans, spyware, adware, and ransomware.
Potential Elements and Functionalities of Malware:
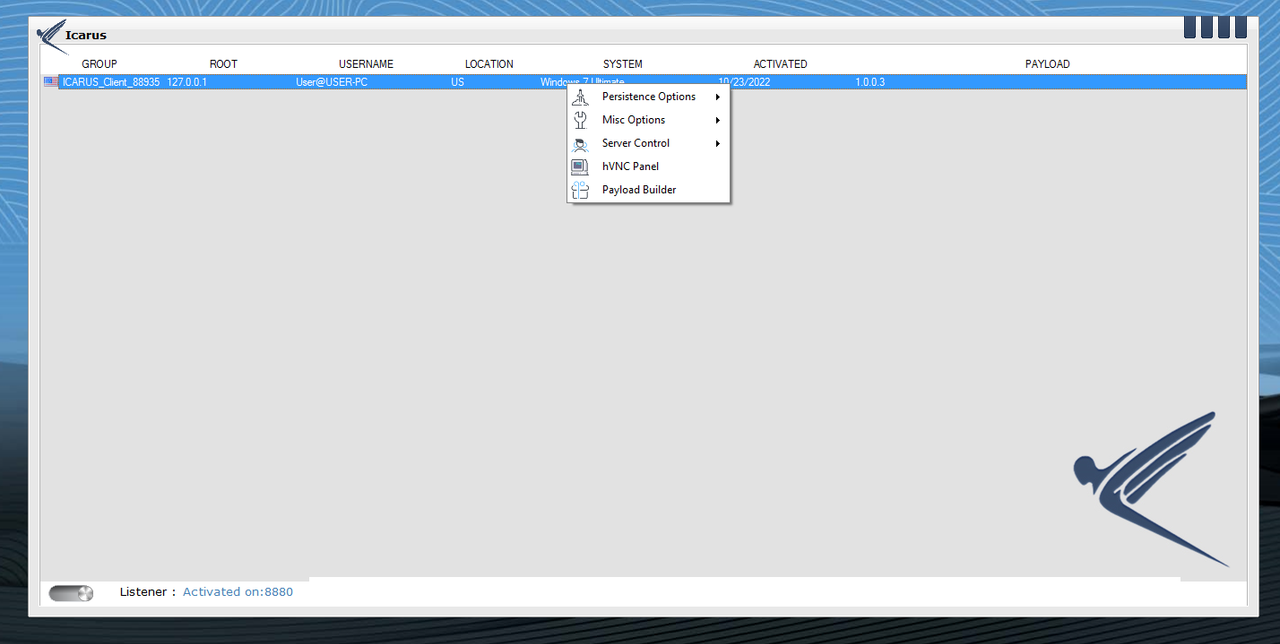
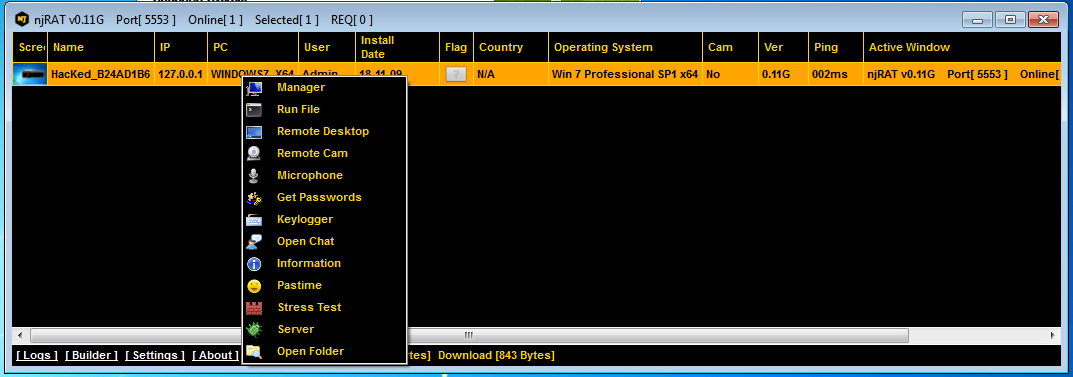
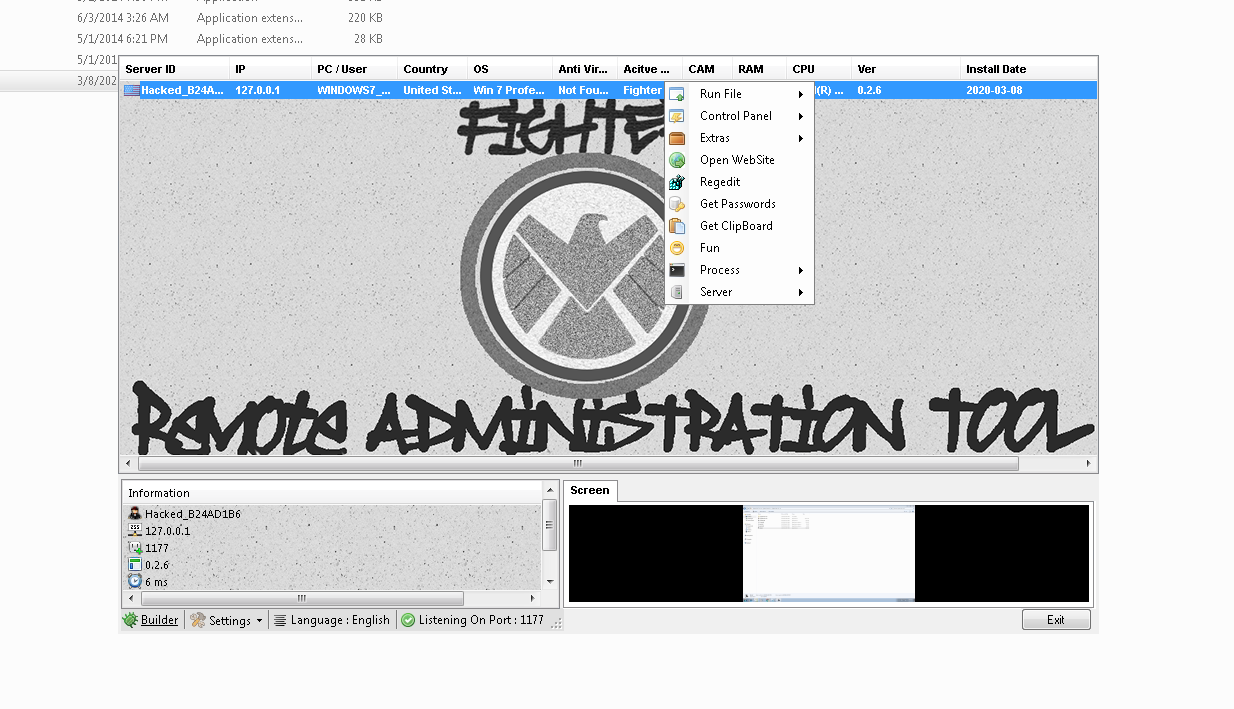
- Remote Access and Control: Malware can grant attackers unauthorized access to an infected system, allowing them to take control remotely. This can lead to data theft, surveillance, or the ability to use the compromised system for various malicious activities.
- Data Theft: Many types of malware are designed to steal sensitive information such as login credentials, financial data, personal documents, and more. This stolen data can then be used for identity theft or sold on the black market.
- Keylogging: Keyloggers are a type of malware that record the keystrokes made by a user. This allows attackers to capture usernames, passwords, and other confidential information as the user types.
- Screen Capture: Some malware can capture screenshots or record the user’s screen, potentially exposing sensitive information or activities.
- Ransomware: This type of malware encrypts a victim’s files or entire system and demands a ransom to provide the decryption key. It can cause significant financial and operational damage.
- Distributed Denial of Service (DDoS): Malware can be used to create a network of compromised devices (a botnet) that can be used to launch DDoS attacks on websites or online services, rendering them inaccessible.
- Propagation: Malware often contains mechanisms for self-replication, enabling it to spread to other systems or devices, infecting a wider network.
- Evading Detection: Malware creators frequently use techniques to avoid detection by antivirus software and security measures, making it harder for victims to identify and remove the malware.
- Persistence: Malware can be designed to maintain a foothold on a compromised system, ensuring it remains active even after system reboots or security updates.
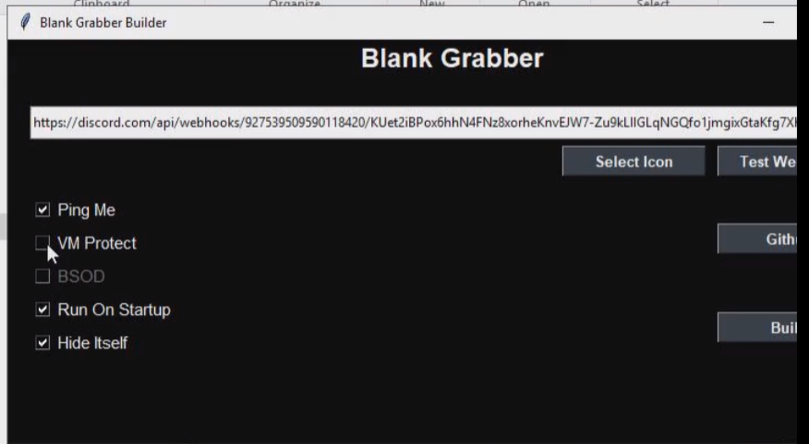
Features
• GUI Builder.
• UAC Bypass.
• Runs on Startup.
• Disables Windows Defender.
• Anti-VM.
• Blocks AV-Related Sites
• Hides/Deletes Itself.
• Custom Message Box.
• EXE Binder.
• Better Obfuscation.
• Anti Unpacking Technique (Removed due to bugs).
• Anti UPX-Detection by YARA (Removed due to bugs).
• Anti Pyinstaller-Detection by YARA (Removed due to bugs).
• Grabs Discord Tokens.
[adinserter block=”1″]
• Injects javascript in Discord client’s files.
• Grabs Passwords from many browsers (Internet Explorer, Mozilla Firefox, Google Chrome, Safari, and Opera.).
• Grabs Chrome Cookies (Netscape format, Importable).
• Grabs Chrome History.
• Grabs Minecraft Session.
• Grabs Roblox Cookies.
• Grabs IP Information.
• Grabs System Info.
• Grabs Saved Wifi Passwords.
• Captures Screenshot.
• Captures Webcam Image (Disabled due to bugs, can be enabled explicitly).
• Sends All Data Through Discord Webhooks.
(…more)
How to Build?
If you literally have no idea how to build it.
Download and install Python 3 (Make sure to enable the Add to PATH option.)
Verify the installation by executing python –version in CMD.
Download Blank Grabber.
Extract the zip file.
Navigate to the Blank Grabber folder and double click Builder.bat file.
Fill in the fields of the builder and press the Build button.