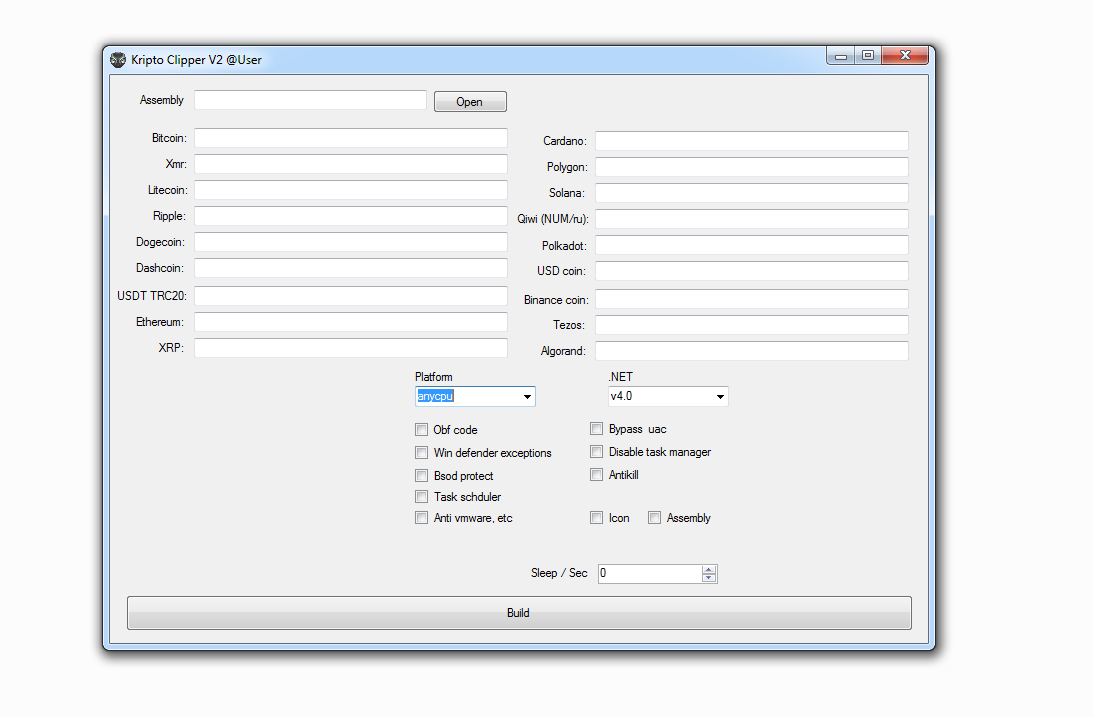
kripto clipper
kripto clipper
Clipboard Monitoring: Crypto clippers operate by monitoring the clipboard of an infected device. When you copy a cryptocurrency wallet address (e.g., a Bitcoin or Ethereum address) to your clipboard, the malware detects this action.
Address Replacement: Once the malware detects a cryptocurrency address in the clipboard, it replaces it with the attacker’s address. This means that when you paste the address into a cryptocurrency transaction, you inadvertently send your funds to the attacker’s wallet instead of the intended recipient.
Stealthy Theft: The victim is often unaware that the address in their clipboard has been altered. As a result, they proceed with the transaction, believing that they are sending funds to the correct recipient.
[adinserter block=”1″]
Functions:
1) Code obfuscation (simple obfuscation)
2) BSOD protect (blue screen of death when process is disabled)
3) Job Scheduler Startup
4) Antikill (process recovery after shutdown (watchdog handler))
5) Exceptions windows defender (resists scanning)
6) Skip virtual environments
7) Disable Task Manager
Supporting cryptocurrencies:
bitcoin
XMR
Litecoin
Ripple
dogecoin
dashcoin
USDT trc20
Ethereum
XRP
Cardano
Polygon
Solana
Tron
Polkadot
USD
Binance
Tezos
Discord: blackhatrussiaofficial#5904
Telegram: https://t.me/adrikadi
DOWNLOAD KRIPTO CLIPPER
KRIPTO CLIPPER
KRIPTO CLIPPER DOWNLOAD LINK