Quasar Rat v1.4.1 Cracked
Quasar Rat v1.4.1 Cracked
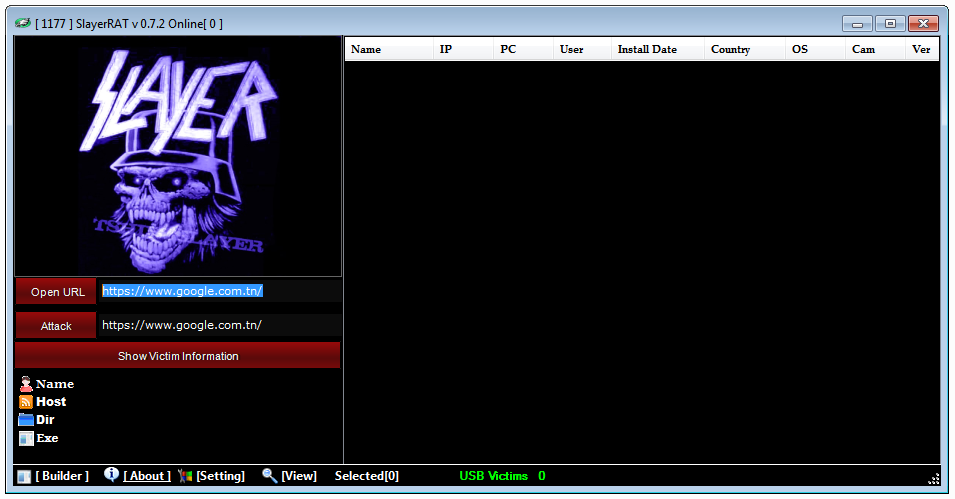
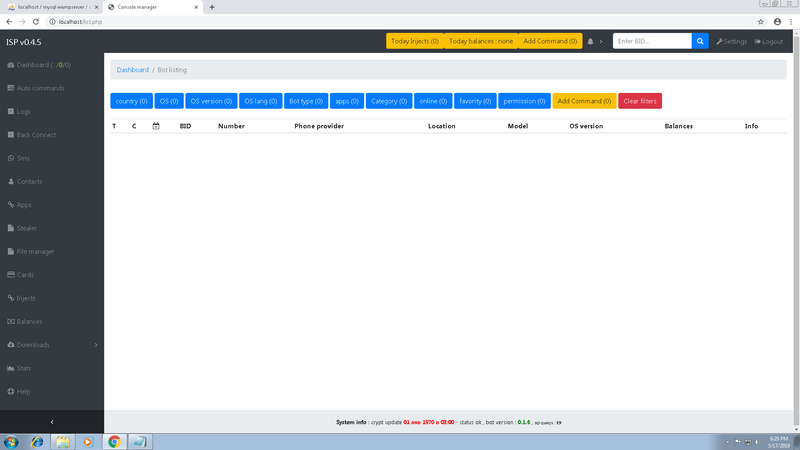
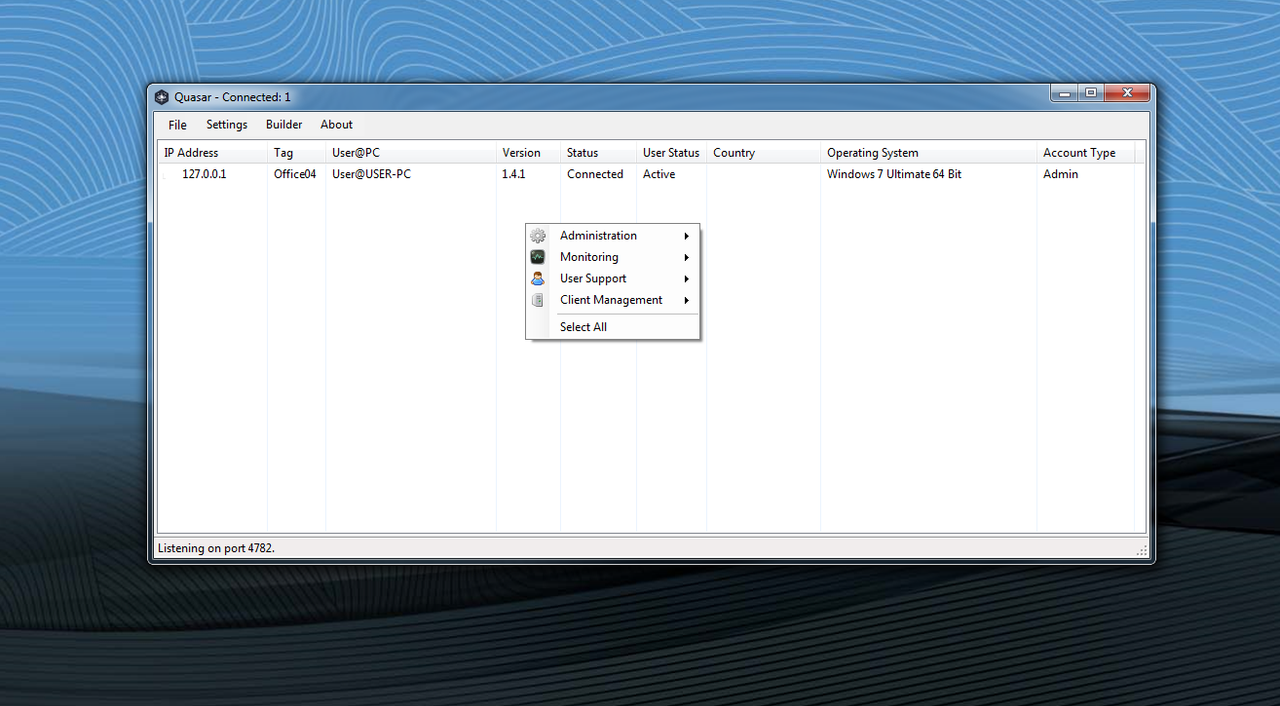
Quasar RAT (Remote Access Trojan) is a type of malware that can grant an attacker remote access and control over an infected computer. This powerful Trojan is a popular tool used by cybercriminals to gain unauthorized access to a victim’s system, steal data, and carry out malicious activities.
Quasar RAT was first discovered in 2015 and has since become a popular choice for cybercriminals due to its wide range of features and ease of use. It is a fully functional remote administration tool that allows attackers to execute commands on an infected computer as if they were physically present in front of the machine.
The Trojan is typically spread through phishing emails, social engineering tactics, or by exploiting software vulnerabilities. Once it infects a system, it can give the attacker complete control over the infected machine. This includes the ability to steal sensitive information, install additional malware, and even use the computer’s resources for malicious purposes.
One of the most concerning aspects of Quasar RAT is its ability to remain undetected by most antivirus programs. The Trojan is often able to bypass traditional antivirus software by using advanced techniques such as code obfuscation and encryption.
[adinserter block=”1″]
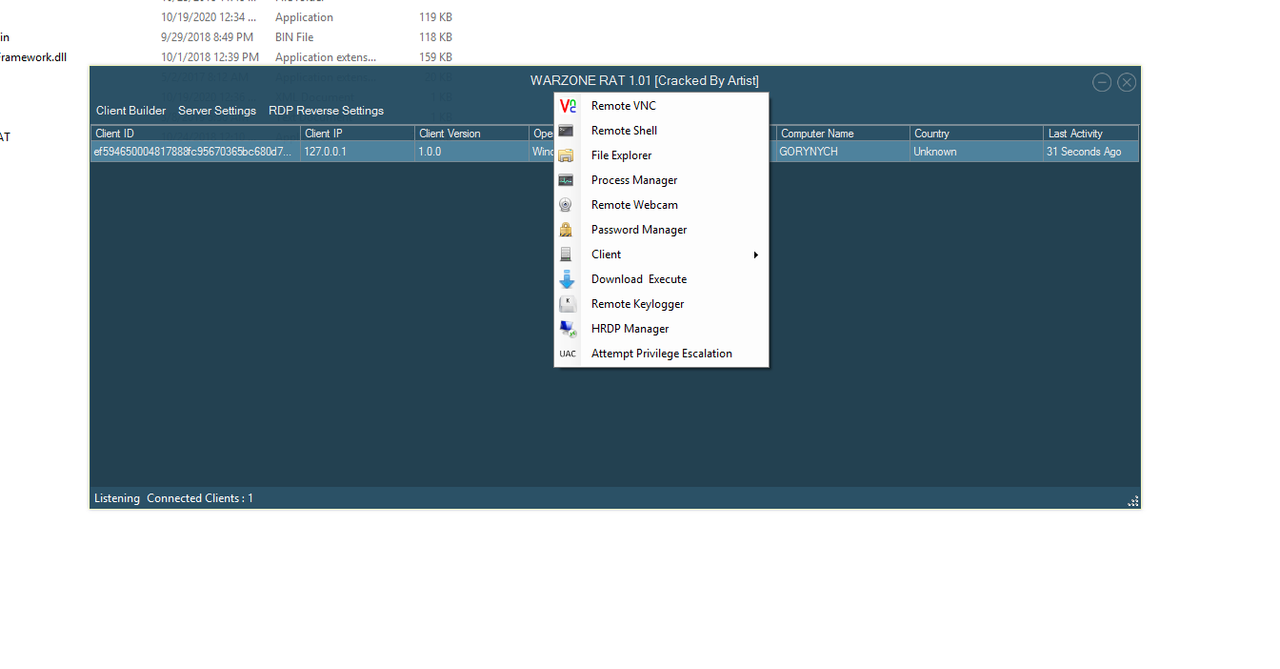
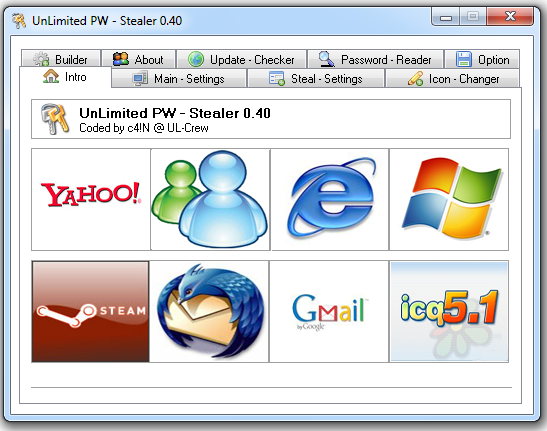
Quasar RAT also comes equipped with a wide range of features, making it a versatile tool for cybercriminals. Some of the features include keylogging, screen capture, file transfer, and remote desktop access. These features allow an attacker to monitor a victim’s activity, steal sensitive data, and carry out further attacks.
To protect against Quasar RAT, it is important to practice good cybersecurity habits, such as keeping software up to date, using strong passwords, and being cautious when opening email attachments or clicking on links. It is also recommended to use a reputable antivirus program that is regularly updated to detect and remove known threats.
In conclusion, Quasar RAT is a powerful and dangerous remote access Trojan that can give attackers complete control over an infected computer. It is important for individuals and organizations to take the necessary precautions to protect themselves against this and other types of malware. Vigilance and caution are key to avoiding falling victim to these types of attacks.
Features
TCP network stream (IPv4 & IPv6 support)
Fast network serialization (Protocol Buffers)
Encrypted communication (TLS)
UPnP Support (automatic port forwarding)
Task Manager
File Manager
Startup Manager
Remote Desktop
Remote Shell
Remote Execution
System Information
Registry Editor
System Power Commands (Restart, Shutdown, Standby)
Keylogger (Unicode Support)
Reverse Proxy (SOCKS5)
Password Recovery (Common Browsers and FTP Clients)
… and many more!
![Arsium Ransomware Builder [ONLY DESKTOP] + Tutorial](https://i.postimg.cc/CLzZGZ2w/download.png)