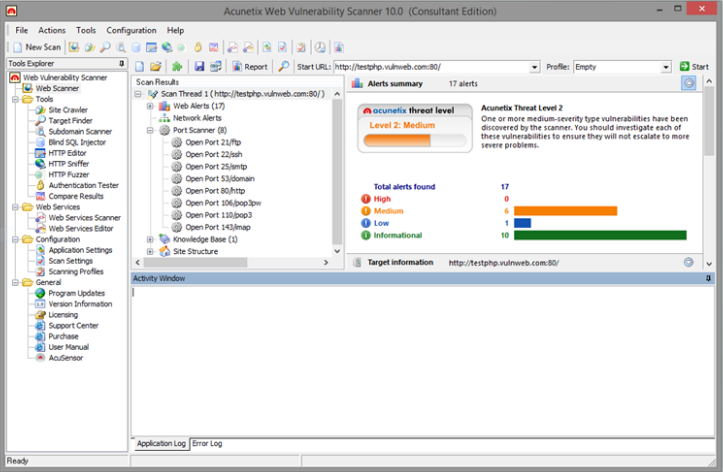
Acunetix Web Vulnerability Scanner v13.0.200217097 for Linux x64
Acunetix Web Vulnerability Scanner v13.0.200217097 for Linux x64
Website security must be a priority in any organization but remains overlooked. Hackers continue to concentrate on web-based applications – shopping carts, forms, login pages, dynamic content, etc. Web applications are accessible 24/7 and control valuable data since they often have direct access to back-end data. Any defense at network security level will provide no protection against web application attacks since they are launched on port 80 – which has to remain open. In addition, web applications are often tailor-made therefore tested less than off-the-shelf software and are more likely to have undiscovered vulnerabilities.
With the uptake of cloud computing and the advancements in browser technology, web applications and web services have become a core component of many business processes, and therefore a lucrative target for attackers. Over 70% of websites and web applications however, contain vulnerabilities that could lead to the theft of sensitive corporate data, credit cards, customer information and Personally Identifiable Information (PII).
Firewalls, SSL and Hardened Networks Are Futile Against Web Application Hacking
Cyber criminals are focusing their efforts on exploiting weaknesses in web applications such as eCommerce platforms, blogs, login pages and other dynamic content. Insecure web applications and web services not only provide attackers access to backend databases but also allow them to perform illegal activities using compromised sites.
Web application attacks are carried out over HTTP and HTTPS; the same protocols that are used to deliver content to legitimate users. Yet web application attacks, both on free open-source software, such as WordPress, Drupal and Joomla!, as well as commercial or custom-built applications, can have repercussions that are the same, or worse than traditional network-based attacks.
The Technology Leaders in Automated Web Application Security
DeepScan Technology allows accurate crawling of AJAX-heavy client-side Single Page Applications (SPAs) that leverage complex technologies such as SOAP/WSDL, SOAP/WCF, REST/WADL, XML, JSON, Google Web Toolkit (GWT) and CRUD operations.
Industry’s most advanced and robust SQL Injection and Cross-site Scripting testing, including advanced detection of DOM-based Cross-site Scripting.
AcuSensor Technology allows accurate scanning further reducing the false positive rate, by combining black box scanning techniques with feedback from its sensors placed inside the source code.
Fast, Accurate, Easy to Use
Multi-threaded, lightning fast crawler and scanner that can crawl hundreds of thousands of pages without interruptions.
Highest detection of WordPress vulnerabilities – scans WordPress installations for over 1200 known vulnerabilities in WordPress’ core, themes and plugins.
An easy to use Login Sequence Recorder that allows the automatic crawling and scanning of complex password protected areas including multi-step, Single Sign-On (SSO) and OAuth-based websites.
Easily generate a wide variety of technical and compliance reports aimed towards developers and business owners alike.
Highest Crawl and Analysis Rate for HTML5 and javascript Security
A fundamental process during any scan is the scanner’s ability to properly crawl an application. Acunetix Vulnerability Scanner features DeepScan Technology; an HTML5 crawling and scanning engine that fully replicates user interaction inside of a browser by executing and analyzing javascript. DeepScan allows accurate crawling of AJAX-heavy client-side Single Page Applications (SPAs) that leverage technologies such as AngularJS, EmberJS and Google Web Toolkit.
Accurately Crawl and Scan with DeepScan Technology
Acunetix Vulnerability Scanner includes Acunetix DeepScan Technology which allows the scanner to robustly test any application, no matter what web technology it’s written in.
At the heart of DeepScan, is a fully automated web browser that can understand and interact with complex web technologies such as AJAX, SOAP/WSDL, SOAP/WCF, REST/WADL, XML, JSON, Google Web Toolkit (GWT) and CRUD operations just like a regular browser would. This allows Acunetix Vulnerability Scanner to test web application just as though it is running inside of a user’s browser, allowing the scanner to seamlesly interact with complex controls just as a user would, significantly increasing the scanner’s coverage of the web application.
DeepScan has been further optimized to analyze websites and web applications developed in Ruby on Rails and Java Frameworks including Java Server Faces (JSF), Spring and Struts.
Hassle-free Authenticated Web Application Testing
Testing authenticated areas of your websites and web applications is absolutely crucial to ensure full testing coverage. Acunetix Vulnerability Scanner can automatically test authenticated areas by recording a Login Sequence using the Login Sequence Recorder. The Login Sequence Recorder makes it quick and easy to record a series of actions the scanner can re-play to authenticate to a page. The Login Sequence Recorder can also record a series of Restrictions; making it trivial to granularly limit the scope of a scan in a few clicks.
Acunetix Login Sequence Recorder supports a large number of authentication mechanisms including
Multi-step/Custom Authentication Schemes
Single Sign-On Authentication
CAPTCHAs
Multi-factor Authentication
Automatic Custom 404 Error Page & Rewrite Rule Identification
Custom 404 error pages are pages that return an HTTP ‘200 OK’ status when a page is not found. Rewrite rules are a set of server-side rules that rewrite requested URLs on the fly.
While still allowing you the flexibility to define rewrite rules and custom 404 pages manually, Acunetix Vulnerability Scanner can automatically detect and configure itself for websites and web applications using custom 404 error pages as well as rewrite rules, saving hours of configuration and increasing the crawl and detection rate.
Manual imports of both Apache HTTP Server and Microsoft IIS rewrite rules are supported.
Highest SQL Injection and XSS Detection Rate
Holistic and accurate vulnerability detection lies in the ability to detect anything from the most obvious to the most obscure SQL Injection, XSS and over 500 other types of web application vulnerabilities. Acunetix is the industry leader in detecting the largest variety of SQL Injection and XSS vulnerabilities, including Out-of-band SQL Injection and DOM-based XSS.
In-depth SQL Injection and Cross-Site Scripting (XSS) Vulnerability Testing
Acunetix Vulnerability Scanner rigorously tests for hundreds of web application vulnerabilities including SQL Injection and Cross-site Scripting. SQL Injection is one of the oldest and most prevalent of software bugs; it allows attackers to modify SQL queries in order to gain access to data in the database. Cross-Site scripting attacks allow attackers to execute malicious scripts inside your visitors’ browser; possibly leading to impersonation of that user.
When it comes to Dynamic Application Security Testing (DAST), while the number of tests a scanner can run is important, it is secondary to how well it can crawl an application – If you can’t crawl it, you can’t scan it! Acunetix Vulnerability Scanner’s DeepScan Technology has the ability to crawl complex client-side Single Page Applications (SPAs), guaranteeing the highest vulnerability detection rate even in client-side vulnerabilities such as DOM-based XSS vulnerabilities.
Advanced Automated DOM-based XSS Vulnerability Testing
DOM-based XSS is an advanced type of XSS attack which is made possible when the web application’s client-side scripts write user provided data to the Document Object Model (DOM). The data is subsequently read from the DOM by the web application and outputted to the browser. If the data is incorrectly handled, an attacker can inject a payload, which will be stored as part of the DOM and executed when the data is read back from the DOM.
DOM-based XSS is often a client-side attack, and the attacker’s payload is never sent to the server. This makes it even more difficult to detect. Acunetix Vulnerability Scanner can scan for a wide range of advanced DOM-based XSS and also provide a stack-trace of the injected payload as it moves inside of the browser’s DOM.
Detection of Blind XSS, XXE, SSRF, Host Header Attacks and Email Header Injection
Traditional methods of detecting vulnerabilities fall short when attempting to detect second-order vulnerabilities; i.e. testing for vulnerabilities that do not provide a response to a scanner during testing. Detection of second-order vulnerabilities requires an intermediary service; Acunetix Vulnerability Scanner, combined with it’s built-in AcuMonitor Technology, makes automatic detection of such vulnerabilities possible and transparent to the user running the scan.
AcuMonitor allows the detection of vulnerabilities such as Blind XSS, XML External Entity Injection (XXE), Server Side Request Forgery (SSRF), Host Header Attacks, Email Header Injection and Password Reset Poisoning.
ICQ:653580170
Whatsapp +79017473945
jabber: russianhackerclub@jabber.ru


![Denial of Service [DOS] Mega Pack](https://i.postimg.cc/rpvMvF66/collage.jpg)