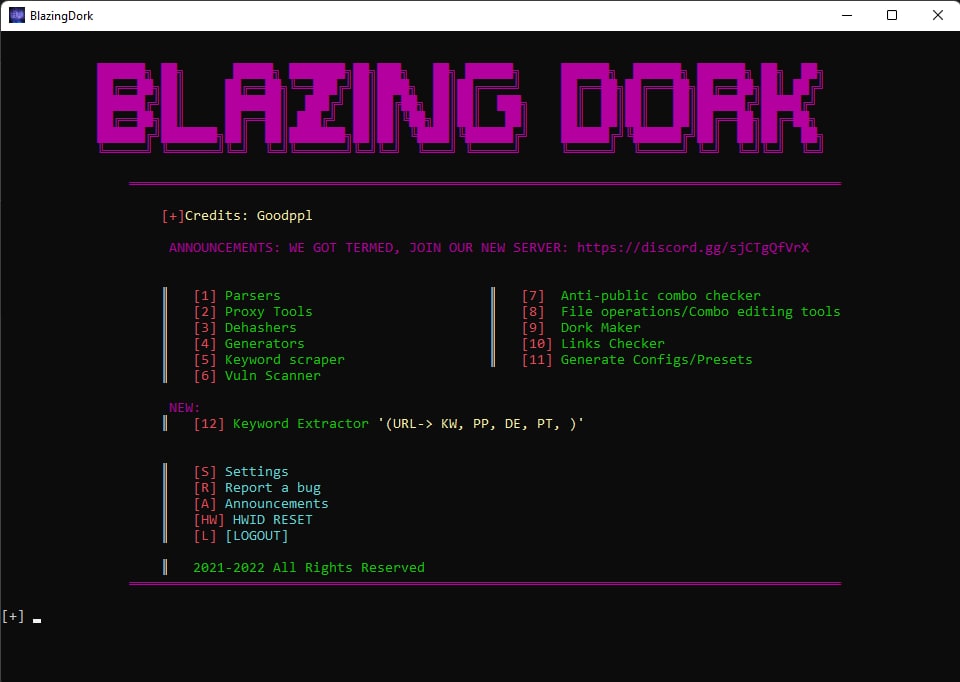
BLAZING DORK V1.5 (NEWEST VERSION) CRACKED
BLAZING DORK V1.5 CRACKED
BLAZING DORK V1.5 CRACKED Google dork query, once in a while simply referred to as a dork, is a search string or customized question that makes use of superior search operators to locate records now not with ease handy on a website. Google dorking, additionally acknowledged as Google hacking, can return statistics hard to come across via easy search queries.
What is a dork query?
A Google dork query, once in a while simply referred to as a dork, is a search string or customized question that makes use of superior search operators to locate records now not with ease handy on a website. Google dorking, additionally acknowledged as Google hacking, can return statistics hard to come across via easy search queries.
Is SQL injection a virus?
This is how SQL injections (or SQLI) happen. The hacker inputs, or injects, malicious SQL code – a structure of malware recognised as the payload – on the internet site and fools it into turning in that code to its database as a respectable query. Hackers use SQL injection assaults to get internal a website’s database.
What is SQL injection in cyber forensics?
SQL injection (SQLi) is a cyberattack that injects malicious SQL code into an application, permitting the attacker to view or adjust a database. According to the Open Web Application Security Project, injection attacks, which consist of SQL injections, had been the 1/3 most serious internet software protection danger in 2021.
How is SQL injection used with the aid of hackers?
SQL injection works via exploiting vulnerabilities in a internet site or pc software – generally thru a information entry form. Hackers kind SQL instructions into fields such as login boxes, search packing containers or ‘sign up’ fields. The intention is to use complicated code sequences to obtain get admission to to a machine and expose the records held inside
What are 5 kinds of SQL injection?
You can classify SQL injections sorts based totally on the strategies they use to get entry to backend information and their harm potential.
In-band SQLi. The attacker makes use of the identical channel of conversation to launch their assaults and to accumulate their results. …
Inferential (Blind) SQLi. …
Out-of-band SQLi.
How SQL injection can be prevented?
The solely certain way to forestall SQL Injection assaults is enter validation and parametrized queries along with organized statements. The software code ought to in no way use the enter directly. The developer should sanitize all input, now not solely net structure inputs such as login forms.
What are the three aspects of SQL?
SQL has three fundamental components: the Data Manipulation Language (DML), the Data Definition Language (DDL), and the Data Control Language (DCL)
What are the four elements of SQL?
The scope of SQL consists of statistics query, facts manipulation (insert, update, and delete), information definition (schema introduction and modification), and facts get admission to control.
What are the two sorts of SQL injection attacks?
Types of SQL injection attacks
Unsanitized Input. …
Blind SQL Injection. …
Out-of-Band Injection.
Can SQL injections be detected?
SQL Injection has come to be a frequent problem with database-driven net sites. The flaw is effortlessly detected, and without problems exploited, and as such, any web page or software program package deal with even a minimal person base is probable to be problem to an tried assault of this kind.
Can SQL be hacked?
To operate an SQL injection attack, the attacker need to first discover inclined consumer inputs in the net web page or application. If a vulnerability exists, such person enter is used at once in an SQL question by way of the internet web page or application. The attacker can create enter content material referred to as a malicious payload
What is known as a dork?
Noun. dork (plural dorks) (derogatory, slang) A quirky, stupid and/or stupid, socially inept person, or one who is out of contact with cutting-edge trends. Often pressured with nerd and geek, however does now not suggest the equal degree of intelligence.
What are Google Dorking methods?
Dorking includes the use of search engines to their full doable to unearth consequences that are no longer seen with a normal search. It lets in you to refine your searches and dive deeper, and with higher precision, into webpages and files that are accessible online.
Which device is nice for SQL injection?
SQLMap is the open supply SQL injection device and most famous amongst all SQL injection equipment available. This device makes it convenient to take advantage of the SQL injection vulnerability of a net software and take over the database server.
FEATURES:
[+] 40+ UHQ MODULES
[+] DORK MAKER
[+] UHQ PROXYSCRAPER
[+] PROXY CHECKER
[+] BLAZING SPEEDS
[+] VULNERABILTY SCANNER
[+] 9 PARSER MODULES
[+] UHQ COMBO EDITOR WITH OVER 12 EDITING MODULES FOR ALL YOUR NEEDS!
[+] FAST DEHASHER
[+] DISCORD NITRO CODE GENERATOR
[+] IPVANISH PROXY GENERATOR
[+] TEMPORARY GMAIL GENERATOR
[+] KEYWORD SCRAPER MODULE WHICH SCRAPES UHQ KEYWORDS FROM PRIVATE API!
[+] ANTI-PUBLIC COMBO CHECKER
[+] FAST UHQ DORK GENERATOR WITH BUILT IN HQ KEYWORDS
[+] HQ LINK CHECKER
[+] CONFIG GENERATOR FOR PARSERS
Whatsapp
Discord: blackhatrussiaofficial#5904
Telegram: https://t.me/adrikadi